VMware vRealize Suite
VMware vRealize Suite, formerly called vCenter Operations Management Suite, is a software platform designed to help IT administrators build and manage heterogeneous, hybrid clouds. The suite itself and all the existing management products were renamed in August 2014.
Components of vRealize Suite
This cloud management suite is made up of several components, including vRealize Automation, vRealize Operations, vRealize Log Insight and vRealize Business for Cloud.
VRealize Automation
VMware vRealize Automation, formerly called vCloud Automation Center, is a software product that offers multivendor and multicloud support. It also allows for IT infrastructure personalization, resource provisioning and configuration, and it automates application delivery and container management.
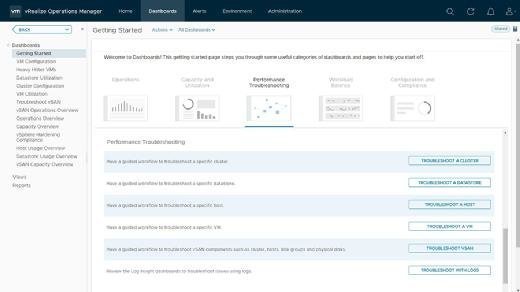
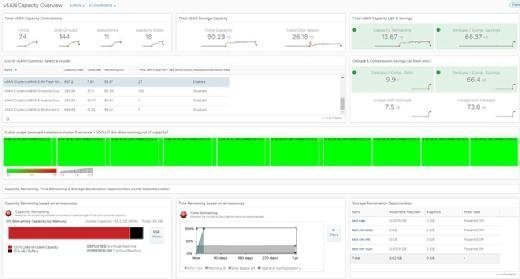
VRealize Operations
VMware vRealize Operations, sometimes referred to as vROps and formerly called vCenter Operations Manager, is a software product that provides operations management across physical, virtual and cloud environments, no matter if those environments are based on vSphere, Hyper-V or Amazon Web Services.
VRealize Log Insight
VMware vRealize Log Insight, formerly called vCenter Log Insight, is a software product with customizable dashboards that allows IT administrators to manage and analyze system log data, troubleshoot issues with vSphere, and perform security auditing and compliance testing.
VRealize Business for Cloud
VMware vRealize Business for Cloud, formerly called IT Business Management Suite, is a software product that provides private and public cloud cost tracking; current and planned workload cost comparison; and consumption tracking and analysis across business groups, applications and services.
VRealize Suite editions
There are three different editions of this platform, offering a mix of vRealize Suite components: the Standard Edition, the Advanced Edition and the Enterprise Edition.
Standard Edition
The Standard Edition includes vRealize Operations for software-defined data center and hybrid cloud management, vRealize Log Insight and the standard version of vRealize Business for Cloud.
Advanced Edition
The Advanced Edition builds on the Standard Edition, with an upgrade to the advanced version of vRealize Business for Cloud and the addition of vRealize Automation for infrastructure.
Enterprise Edition
The Enterprise Edition builds on that foundation even further by adding vRealize Automation for applications and vRealize Operations for application monitoring.
VRealize Suite Pricing
VRealize Suite pricing depends on the edition that's being purchased, but in general, it's based on a Portable License Unit (PLU). One PLU allows an administrator using vRealize Suite to manage an unlimited number of on-premises operating system instances on a vSphere CPU or up to 15 public cloud operating system instances. The Standard Edition is $3,745 per PLU, the Advanced Edition is $6,245 per PLU and the Enterprise Edition is $7,745 per PLU.
VRealize Suite is packaged with VMware vSphere Enterprise Plus in vCloud Suite and offered at a discounted rate compared to purchasing vRealize Suite and VMware vSphere Enterprise Plus separately.
Add-ons
Some add-ons to vRealize Suite include vRealize Code Stream, vRealize Orchestrator and vRealize Infrastructure Navigator.
VRealize Code Stream
VRealize Code Stream is a product that automates the delivery of new applications and updates.
VRealize Orchestrator
VRealize Orchestrator, formerly called vCenter Orchestrator, is a workflow engine that integrates with vRealize Suite and vCloud Suite.
VRealize Infrastructure Navigator
VRealize Infrastructure Navigator, formerly called vCenter Infrastructure Navigator, provides a comprehensive view of the application environment.